Thinking
beyond the
perimeter.
A cybersecurity breach isn't just a technical failure; it's a narrative of vulnerability. Our mission is to rewrite that story before it happens.
From initial recon to full compliance restoration, we walk the path of the attacker to protect your assets.
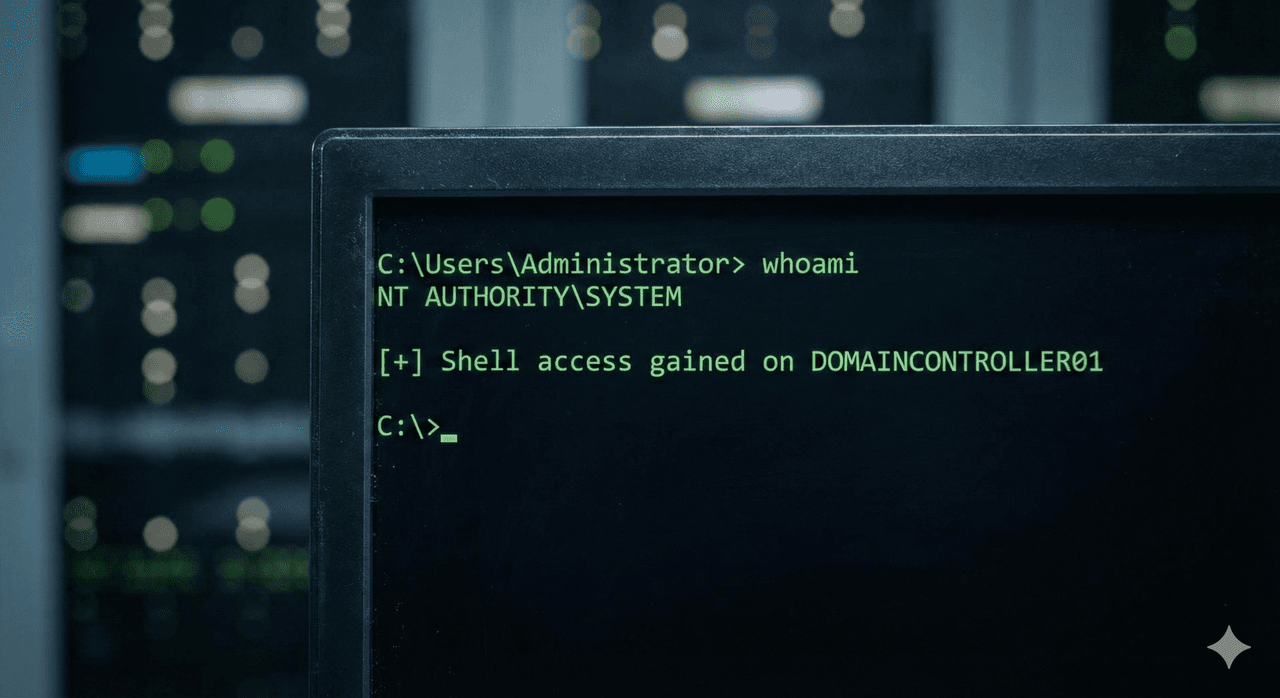
01. The Pentest
Vulnerability Mapping
We conduct thorough penetration tests to identify the weakest links in your perimeter, applications, and human factors.
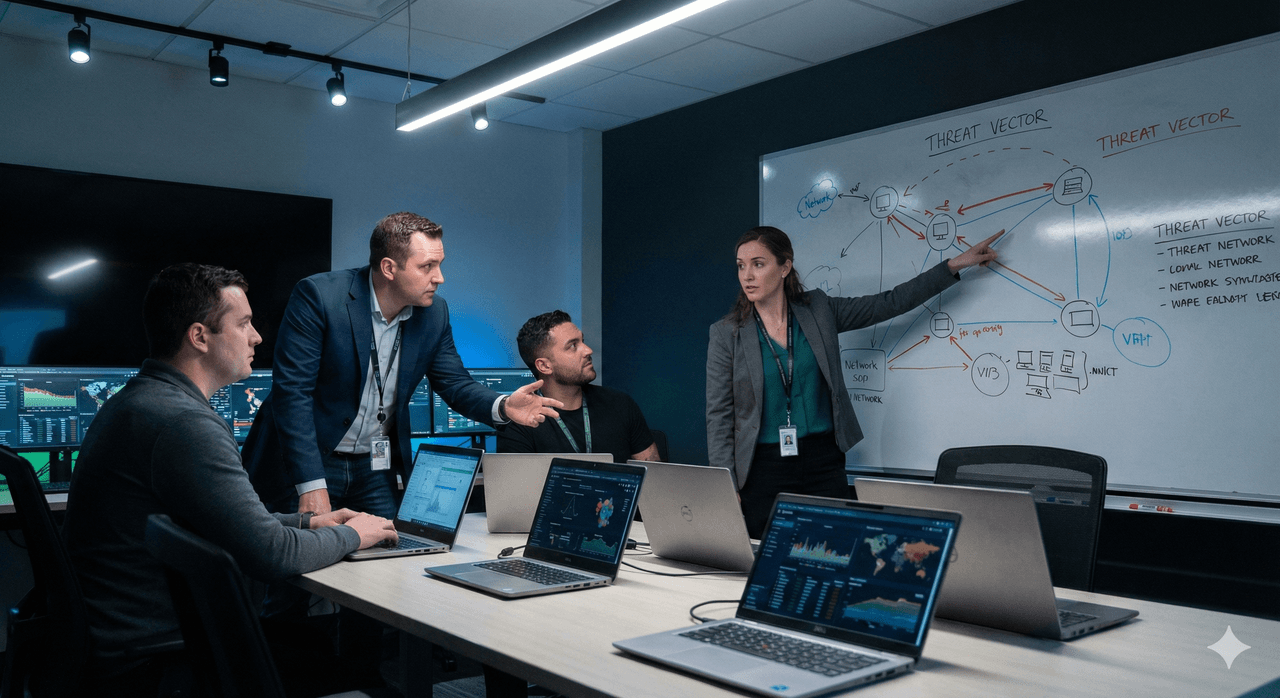
02. Breach Simulation
Response & Detection
We demonstrate exactly how threat actors move laterally and how to implement detection mechanisms to neutralize them.
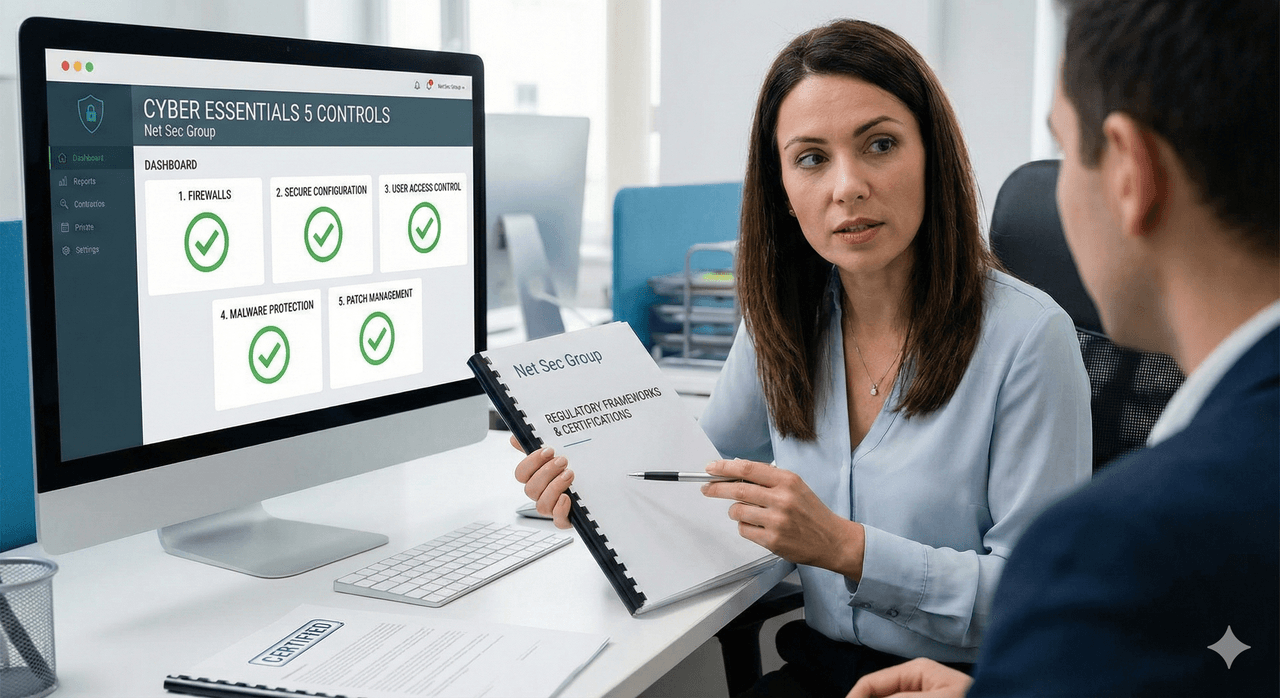
03. Compliance
Certified Protection
Translating technical safety into regulatory assurance. From Cyber Essentials to industry-specific auditing.
Your Story Ends with Security.
Don't wait for a headline to take action. Start your security assessment today.
Get Started

